Secure use of your mobile phone on the company network
More and more mobile devices are connecting to company networks. How can you make sure that everyone can work securely?

Employees are increasingly using mobile devices, with wireless access to the company network. This presents challenges in the areas of security and management. A complete, user-friendly solution ensures that everyone can work securely on mobile devices.
Smartphones, tablets and laptops have quickly earned their place on the work floor. The figures show that this trend will continue to grow in the years to come. More than three-fourths of all Internet traffic already originates from mobile devices, and that share will only continue to increase. Some experts even expect desktops to become obsolete.
IT department blues
That trend is logical: technological advances keeping making it even easier to connect mobile devices to the company network via Wi-Fi. Employees are also more productive and more satisfied with their work when they are not bound to a permanent workplace at the office but can do their work at any time, from any place. However, in addition to the advantages this offers, it is seriously worrisome for the IT department. Administrators must deal with an increasing number of different devices, each with their own operating system and security settings. That variation is primarily a result of the fact that many organisations allow employees access to the company network through their smartphones, tablets or laptops: Bring Your Own Device.
One-fifth of all organisations in the world have had to deal with breaches of their mobile security.
The risks of allowing mobile devices access to the company network
Organisations are already very aware of the need for firewalls, anti-malware solutions and back-ups. This holds less true for mobile security. A recent study showed that throughout the world, twenty percent of all organisations have had to deal with at least one breach of their mobile security. The same study showed that the security risks of employees’ mobile devices place a heavy load on the shoulders of the IT department.
In fact, more and more threats – phishing, spyware, ransomware, Trojan horses and other malware – are being directed at mobile devices. Not knowing what is happening on unsecured mobile devices can cause serious problems.
- Malware can gain access to the company network via those devices.
- Infected devices can infect the network and other devices.
- Privacy-sensitive data may end up on the street.
- Using certain apps too intensively can slow down the company network.
Complete solution for access and security
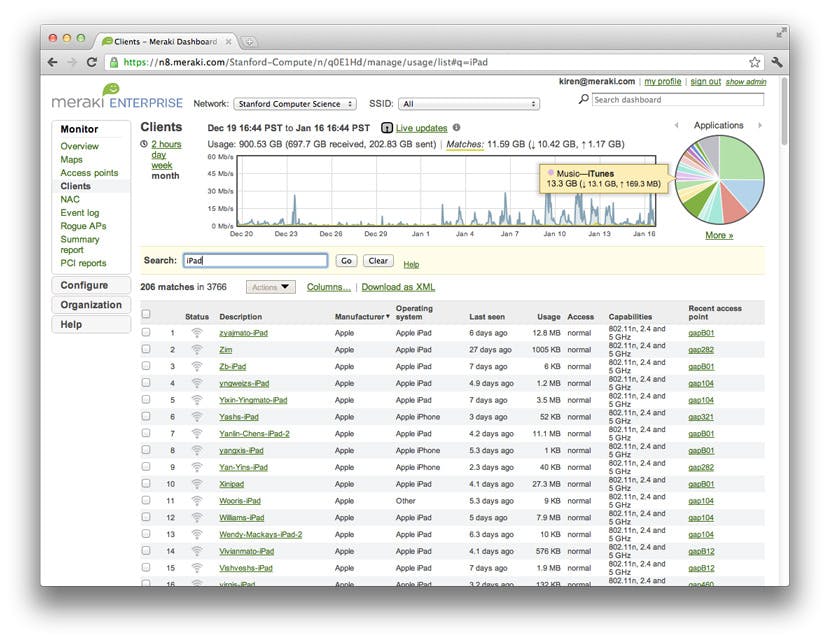
If you want to know exactly which mobile and other devices are active on your company network and manage their use via the cloud, you will need a solution that is both user-friendly and easy to expand. With Cisco Meraki access points, you can manage all of your organisation’s network devices centrally in the cloud. Security incidents can be immediately identified and resolved with a single click. The network can easily be expanded with support equipment, such as additional access points, switches, IP cameras and other security appliances.
The benefits:
- A single, central dashboard for managing users, applications and devices. Even when you have multiple access points and other equipment. Automatic monitoring and warning gives you constant insight into the details of what is happening. Wherever you are.
- There is no need to install and maintain hardware and software for management.
- Secure, PCI-compliant cloud infrastructure. Scalable from small companies to millions of users.
- Security is so strong that insurance is available against hacking, because insurers have faith in this solution.
Want to add an additional security layer? Cisco Umbrella is a cloud-based security platform that secures your network on the level of the DNS server. This means that 99 percent of all cyber attacks for spreading malware can be stopped in good time. Umbrella can be used in combination with Meraki.




